Connected devices, such as smartphones and wearables are now undoubtedly the most important and prevalent consumer devices in our lives. These machines interweave with a vast world of other connected objects that work together to improve and connect our lives. They help control and protect our homes, unlock and control our cars, and monitor our health, just to name a few use cases.
However, as brilliant as these innovations are, they are not perfect… at least the ecosystem is not yet perfect. The solutions and technology available often operates in separate silos and some use cases struggle to work in sync with others.
As an example, we can look at how smart home devices don’t always pair easily with apps, hubs or other similar systems. It’s crucial that important players in this space work together and commit to improving interoperability so that consumer experiences become holistic and unified. If we don’t all work together and improve this, we may find consumers become increasingly disappointed or alienated by the products they’ve become so attached to.
To help guide us and to see what the future may hold, we commissioned wide-ranging research projects assessing how consumers visualize their ideal experience in this connected world. Since the beginning of 2016, we’ve reached out to over 5,000 consumers across nine countries to discover more about their thoughts and experiences. The results give us valuable insights into what consumers want (and will want) from the connected object ecosystem, as well as what OEMs (Original Equipment Manufacturers), retailers and OTTs (Over-the-top) service providers need to bear in mind.
As we surveyed consumers, three key areas kept coming up:
- Trust in connected objects
- A strong need for a unified/seamless consumer experience
- Service personalization
To help illustrate the findings and give us a clear idea of what ‘the people’ want, we’ve created two personas that represent our audience. Time to meet Emma and Paul…
Both Emma and Paul have their fingers right on the pulse of technology – they know the market available to them and have high hopes for the future. To give us an idea of what Emma and Paul expect, see below for some examples and snapshots.
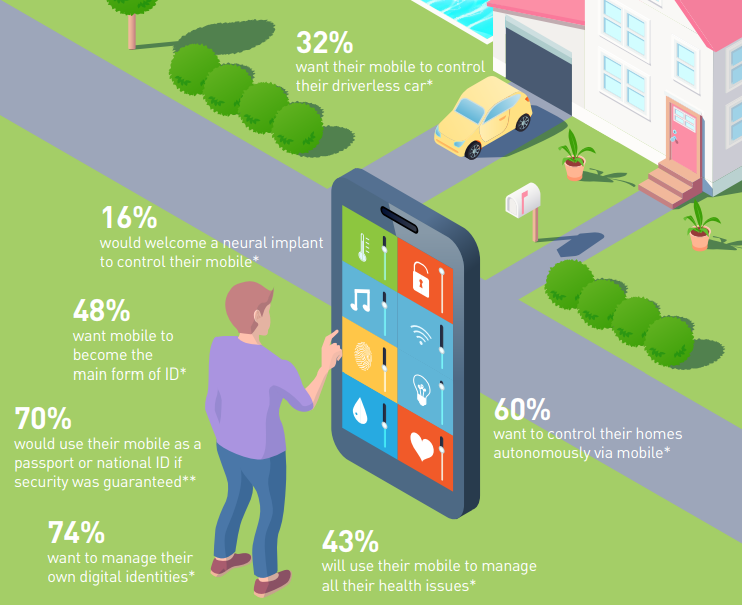
Let’s start with a key representative insight from the data, from Emma. She represents the many consumers that want a unified experience which allows them to control multiple areas of their life form the comfort of their own palm.
We therefore must consider that for a smartphone to be at the center of connected life, all key stakeholders must work together. It’d be impossible for this to be achieved without cooperation. However, the onus of responsibility may lie most strongly with handset manufacturers here as almost half (46%) if consumers believe these OEMs will have the biggest influence over the mobile experience in the future (2025).
But it’s not just control from smartphones desired by consumers… Paul wants his phone to work as his ID. This sort of use case can already be seen in Colorado right now where they’ve been running a live pilot scheme, testing Digital Drivers Licenses. Once again, for this to happen, more cooperation will be needed.
Another key highlight of the findings is the importance of privacy, particularly the segregation of data; consumers want to control who has access to what, easily and securely, without fuss. This expectation is achievable, especially if we bear in mind how Emma wants a single contract for all her connectivity.
Consumers are also expecting a full embrace of biometrics. As part of a seamless mobile experience, consumers want biometric techniques such as fingerprint and facial recognition to be a prominent feature. They also expect mobile security to be seamless (60%).
Furthermore, when it comes to unlocking their devices in the future, consumers believe that biometric authentication will rely new forms. 40% think voice biometrics will be available; a similar proportion (43%) also think iris scans will become mainstream. As you can see, ‘seamless’ is a key word for the consumers of today and tomorrow, and it’ll only be possible with cooperation between all key parties.
These are of course just a few examples; for more information on what consumers expect, make sure you read our easy-to-read report.
This post originally appeared on the Gemalto blog and is reused with kind permission.
Download the Gemalto report now – Internet of things (IoT): what do consumers want from their connected future?
Consumer IoT and smartphones have become the most important consumer devices in our lives. And behind this is a vast world of connected objects that mesh together to improve our lives.
Over the past 18 months we’ve spoken to 5,000 people from nine countries about what they want from their future mobile and IoT experience. The findings are fascinating and complex, containing valuable insights that we are pleased to share with everyone involved in the mobile and connected object ecosystem; the device manufacturers, the retailers, the OTT service providers.